On May 7, 2019, Baltimore was hit with a ransomware attack. The hackers took control of the city's computer systems and demanded about 13 bitcoins. The value of bitcoins varies, but the demanded ransom is somewhere in the neighborhood of $100,000. Baltimore officials refused to pay the ransom and the city battled the impacts for weeks. Thankfully, the attack did not affect emergency services, but residents were impacted in multiple ways with nearly every city service touched by the cyberattack. (Click here to see the full list.) Here are a few examples of how city functions were impacted: residents were unable to pay speeding tickets, parking fines and tax bills. Baltimore was unable to create and mail water bills. The real estate market was also put on hold because no one was able to buy or sell real estate for two weeks until a paper workaround was developed.
The lost and delayed revenue along with the direct costs of recovering from the ransomware attack is estimated to be more than $18 million. To make matters worse, Baltimore does not have any insurance to cover a cyberattack.
Lingering impacts
More than a month later, Baltimore’s data was still being held hostage. The city is slowly making progress, but the impacts of the ransom attack will likely linger for months. As of June 10, 65 percent of public employees had regained access to their computer. At that time, Baltimore remained unable to create and mail water bills. (All late fees and penalties are being waived until the online system is back online.) Manual work arounds have been created for some processes, but online resources remain unavailable, and many city services are still halted or functioning in a limited way.
How did this happen?
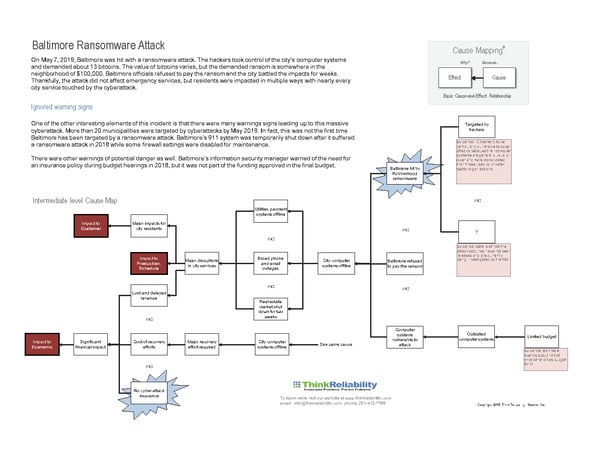
How does a cyberattack so dramatically impact a major American city? The ransomware attack is currently the subject of an FBI investigation, so few details about how the actual attack was conducted have been released, but there is still quite a bit of interesting information available. An initial Cause Map™, a visual method for performing a root cause analysis, can be built to capture what is currently known. The causes that contributed to an issue are laid out visually to intuitively show the cause-and-effect relationships. During an ongoing investigation, the Cause Map™ can be used to document all currently known information, as well as keep track of where additional information is needed to thoroughly understand the incident. As more information becomes available, more detail can be added to the Cause Map™.
The media has reported that the ransomware used was RobinHood, which is extremely powerful and considered to be unbreakable. Without a digital key to unlock the ransomware, Baltimore is not able to access the data held hostage and will have to rebuild their computer servers. Learning from the Baltimore experience may help other cities protect themselves from a similar attack, or at least better understand the consequences and what it takes to rebuild electronic infrastructure when one occurs.
Statements by city officials have indicated Baltimore had outdated computer systems, software and hardware, which made it more vulnerable to a cyberattack. Cyber security experts have stated that Baltimore is not the only city with outdated computer systems and that municipalities tend to be particularly vulnerable to cyberattacks because their computer systems are generally older and more complicated than those used by private-sector organizations. Understanding the details of what makes a computer system vulnerable and what resources are needed to keep it secure could help other cities determine how much to budget toward information technology and cybersecurity. Also, understanding the expense associated with such an attack may help other cities to determine if paying for cyberattack insurance is a worthwhile investment or not.
Ignored warnings
One of the other interesting elements of this incident is that there were many warnings signs leading up to this massive cyberattack. According to NPR, more than 20 municipalities had been targeted by cyberattacks by May of this year. It is still a relatively low percent of municipalities that have been impacted, but it is still a realistic potential risk. In fact, this was not the first time Baltimore was targeted by a ransomware attack. Baltimore’s 911 system was temporarily shut down after it suffered a ransomware attack in 2018 while some firewall settings were disabled for maintenance.
There were other warnings of potential danger as well. Baltimore’s information security manager warned of the need for an insurance policy during budget hearings in 2018, but it was not part of the final, approved budget. Insurance is always tricky—you don’t want to pay for unnecessary insurance, but it can mitigate the financial impact of an incident. Having a good understanding of both the potential impacts (consequences) of an incident and the likelihood (probability) of something occurring can help determine whether or not insurance is a worthwhile use of resources.
Planning ahead
Obviously, it is always easier to see the warning signs after an incident occurred. There are always budget limitations and other competing resource priorities. One thing we can do is to educate ourselves about potential risks is to study and learn from incidents while being on the lookout for warning signs. Rarely does a large incident occur without any prior notice. Pay attention to where smaller incidents are occurring within your own organization. Are there any patterns or particular areas where problems are occurring? Stay up-to-date on what incidents happen at other sites or in similar industries and try to determine if your organization has similar vulnerabilities. Working to thoroughly understand the risks facing your organization can help you determine the most effective way to use your resources to mitigate them.